Yes, RemotePC offers secure and optimized solutions for accessing remote computers. RemotePC uses TLS v 1.2/AES-256 encryption for transferring user authentication data between remote computer and local computer. Personal Key, a unique password set for each computer, acts as an extra layer of protection.
Yes, RemotePC allows you to share your computer over any kind of Internet/LAN connection and even any firewall/proxy server.
Your computer can only be accessed if you share your session code with another person. Without knowing the session code, it is not possible to access your computer. Do not share the code with a person you do not trust.
Personal Key acts as a secondary password to access each computer. It is a password set by you and acts as your computer's unique access code. It is stored only on your computer and not on the RemotePC servers. Whenever you try to access any remote computer, you will be prompted to enter the personal key.
RemotePC uses TLS v 1.2/AES-256 encryption for securing data transfers between local and remote computers during remote sessions.
Yes. RemotePC uses TLS v 1.2/AES-256 encryption on data transmission during remote access.
We will never call you asking for login information, requesting payment or any other such information. If you receive a call of this nature, it is probably a phishing attempt. During such a scenario, do not share any information, and immediately contact us for quick assistance.
Yes, it may be a possibility that your ISP is blocking RemotePC and other remote access services. TalkTalk, based in the UK is one such ISP. Situations like these can be resolved by changing the router settings to use primary and secondary servers other than those of TalkTalk. For example, you can use Google's Public DNS IP addresses like 8.8.8.8.
RemotePC assists users in achieving compliance to the benchmarks laid out under the Federal Information Processing Standards (FIPS) validation for cryptographic products/software used in the USA. RemotePC uses FIPS approved encryption algorithms and adheres to physical security.
We are currently blocking access from the following countries for security and compliance reasons:
- Russia
- China
- Ukraine
Paid users from these countries can send request for allowing IPs but each request is subject to review and may not be approved. If your IP address changes frequently, you will need to provide updated information for consideration.
For more assistance, contact our support team.The two-factor authentication process enhances the security of your account and prevents access by unauthorized parties. Once two-factor authentication is enabled, in addition to your password, you will need to enter a verification code sent to your registered email address or phone number, while logging in to RemotePC.
To enable two-factor authentication,
- Login to RemotePC via web browser and click your username at the top-right of the screen.
- Select 'My Account' and navigate to the 'Security' tab.
- In the 'Two-factor authentication' section, click 'Enable'.
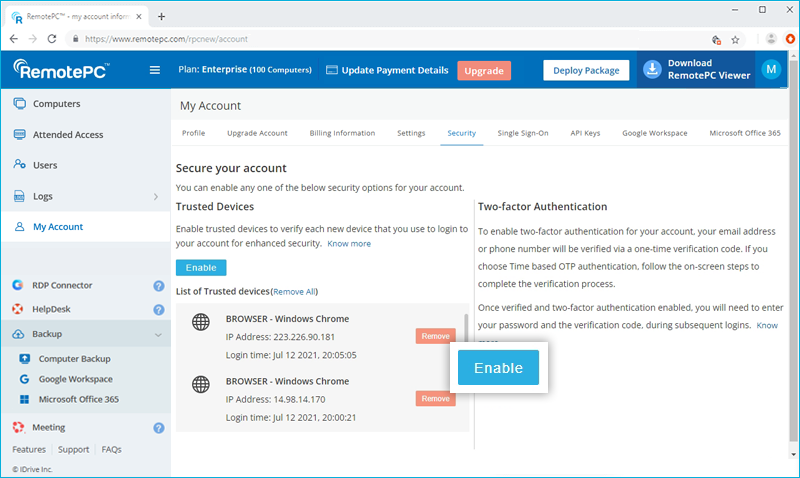
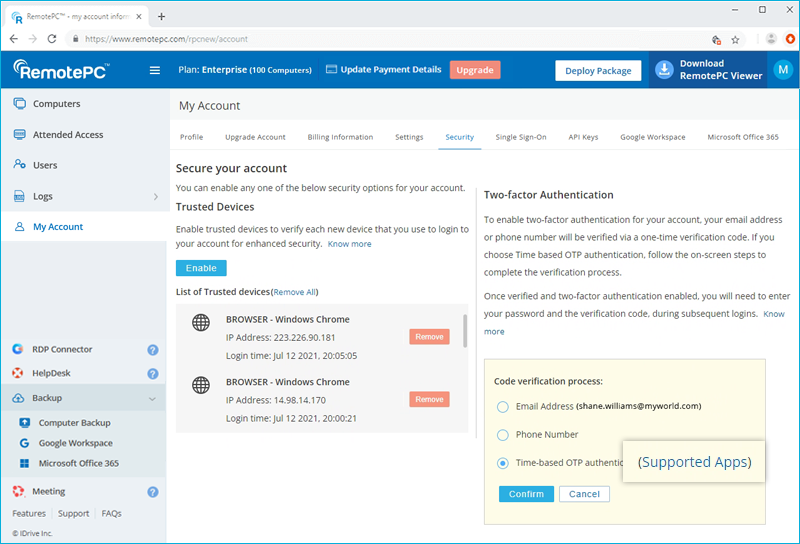
- Select 'Email Address', 'Phone Number' or 'Time based OTP authentication' as your preferred method of receiving the one-time verification code and click 'Confirm'. If you have chosen 'Phone Number', enter the same and click 'Send Code'. Click here to know how to set up via Time-based OTP Authenticator app.
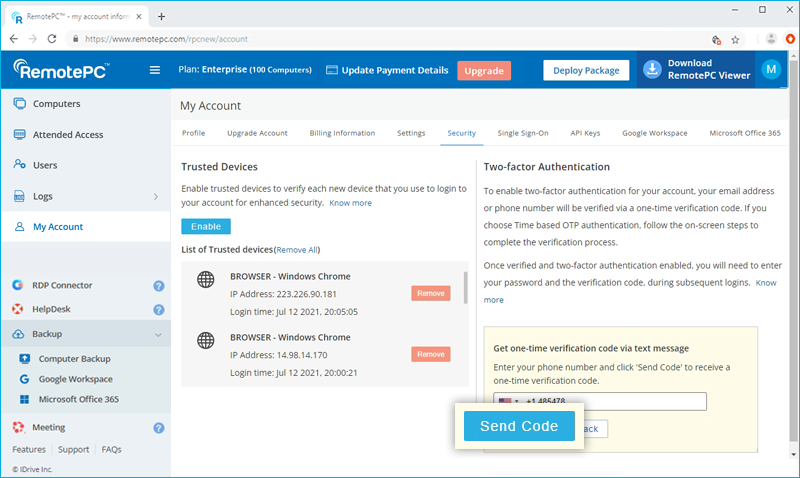
- Enter the verification code sent to your registered email address or phone number and click 'Verify & Enable'.
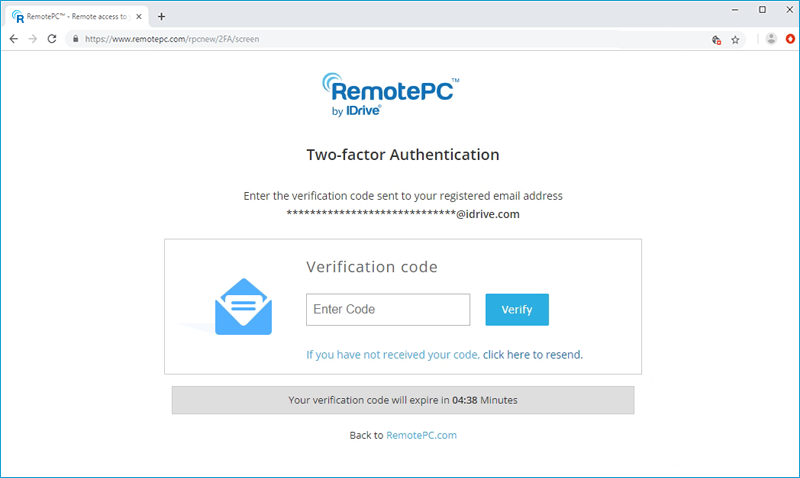
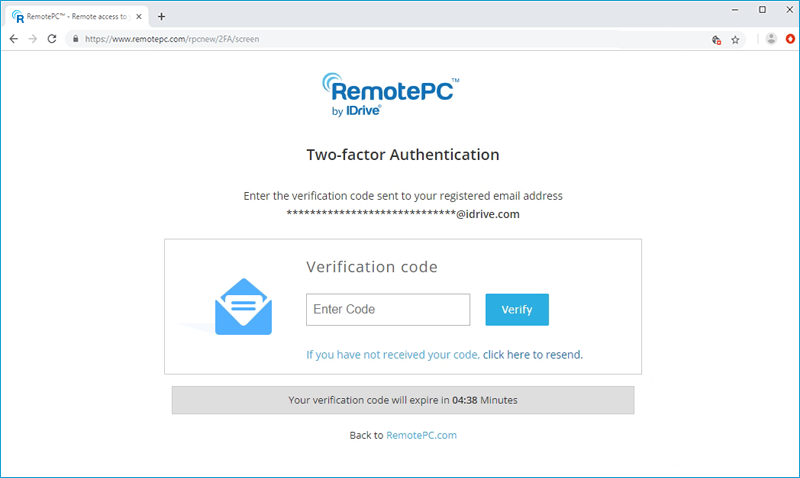
To login after two-factor authentication is enabled,
- On the login screen, enter your username and password and click 'Login'.
- You will be prompted to enter a verification code sent to your email address or phone number.
- Enter the code and click 'Verify'.
How do I set up two-factor authentication for my RemotePC account with Time-based OTP authentication?
The two-factor authentication process enhances the security of your account and prevents access by unauthorized parties. Once two-factor authentication is enabled, in addition to your password, you will need to enter a verification code generated by the Time-based OTP authenticator app, installed on your mobile device, while logging in to RemotePC.
To enable two-factor authentication,
- Login to RemotePC via web browser and click your username at the top-right of the screen.
- Select 'My Account' and navigate to the 'Security' tab.
- In the 'Two-factor authentication' section, click 'Enable'.
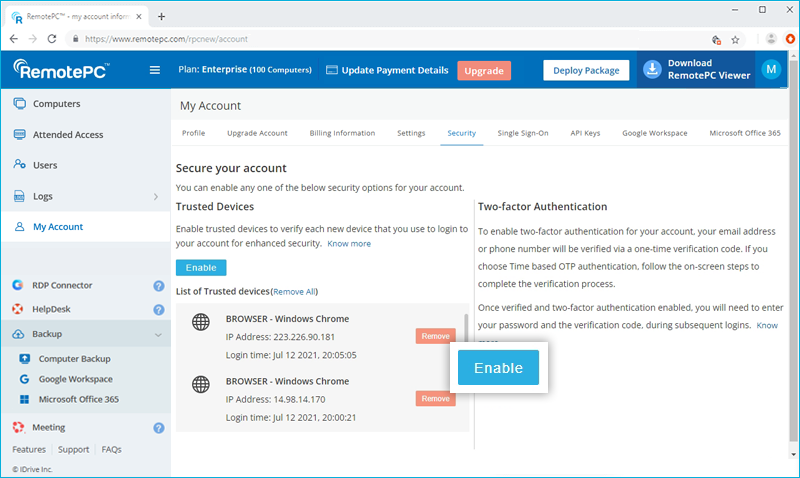
- Select 'Time based OTP authentication' as your preferred method of receiving the one-time verification code and click 'Confirm'.
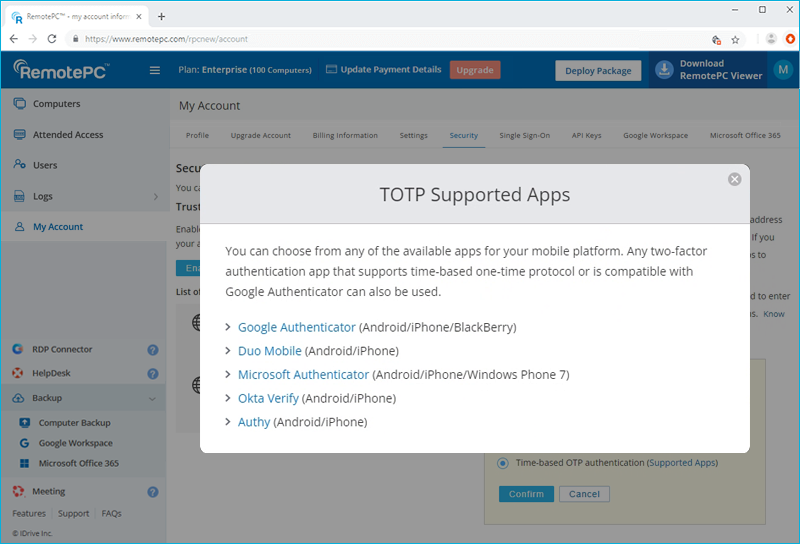
See supported TOTP apps
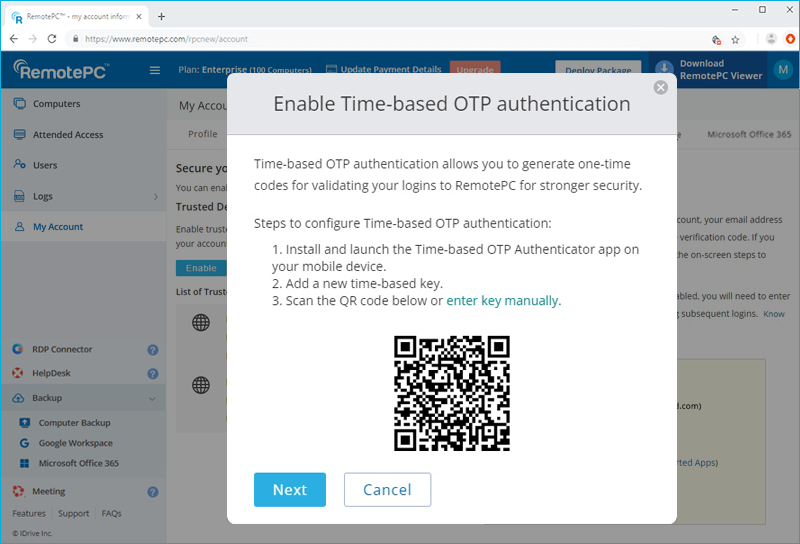
- Launch the Time-based OTP authenticator app on your mobile device and scan the QR code displayed on your computer screen. Alternatively, you can also view the key by clicking on 'enter key manually' and type it manually on your mobile device and click 'Next'.
- Copy and save the recovery code displayed on your computer screen securely or click 'Download' to download and save as a .txt file. Click 'Continue'.
Note: You will require the recovery code to deactivate two-factor authentication for your account, in case you lose access to your mobile device where the Time-based OTP Authenticator app is installed.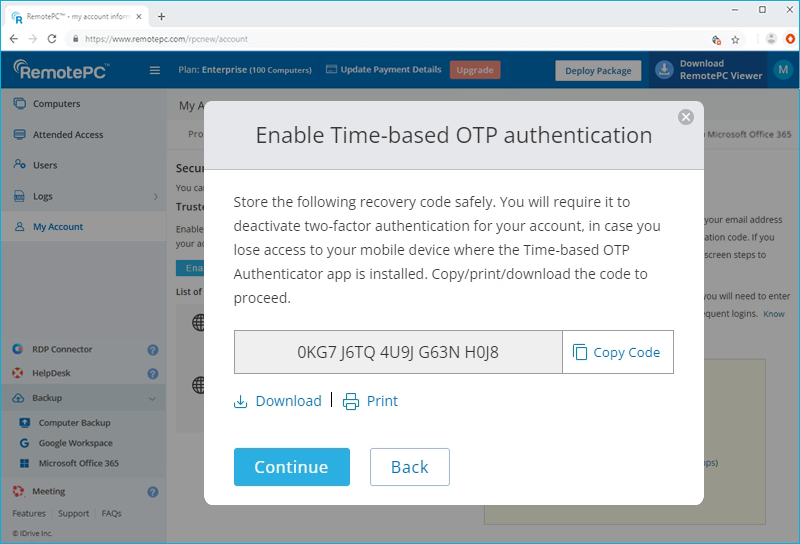
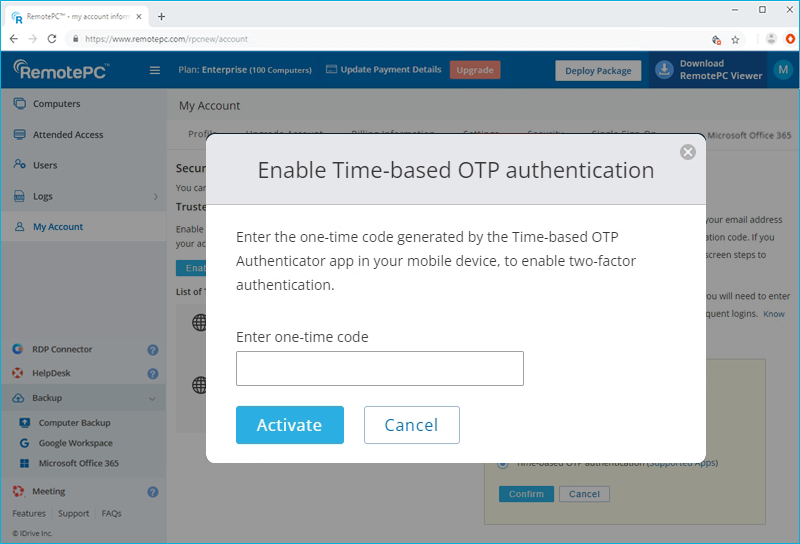
- Enter the one-time code generated by the Time-based OTP Authenticator app in your mobile device and click 'Activate'.
To login after two-factor authentication is enabled with Time-based OTP Authenticator,
- On the login screen, enter your username and password and click 'Login'.
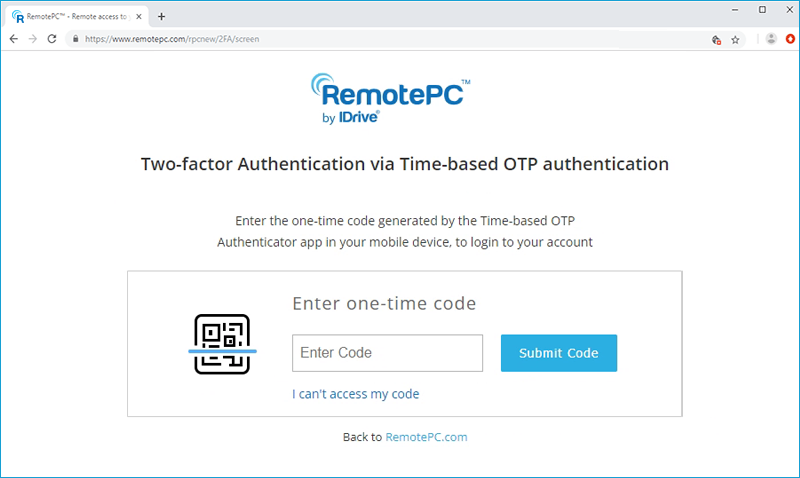
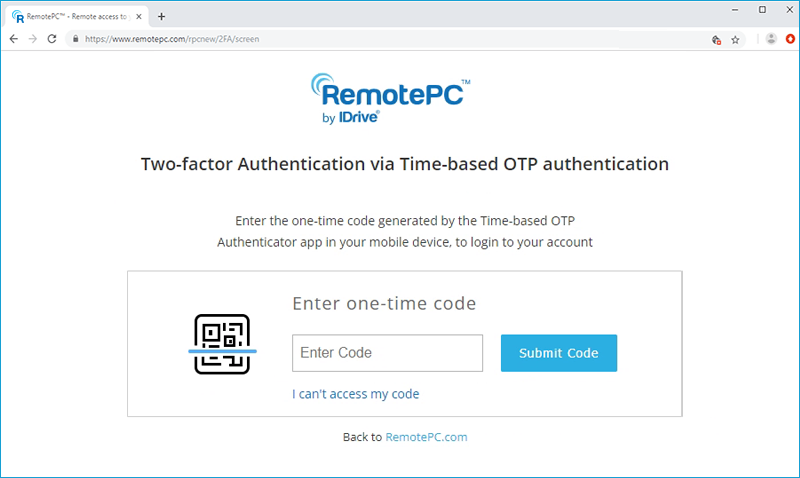
- You will be prompted to enter the one-time code generated by the Time-based OTP Authenticator app in your mobile device.
- Enter the code and click 'Submit Code'.
RemotePC supports the following Time-based OTP authenticator apps:
- Google Authenticator (Android/iPhone/BlackBerry)
- Duo Mobile (Android/iPhone)
- Microsoft Authenticator (Android/iPhone/Windows Phone 7)
- Okta Verify (Android/iPhone)
- Any other authentication app that supports time-based one-time protocol, or compatible with Google Authenticator
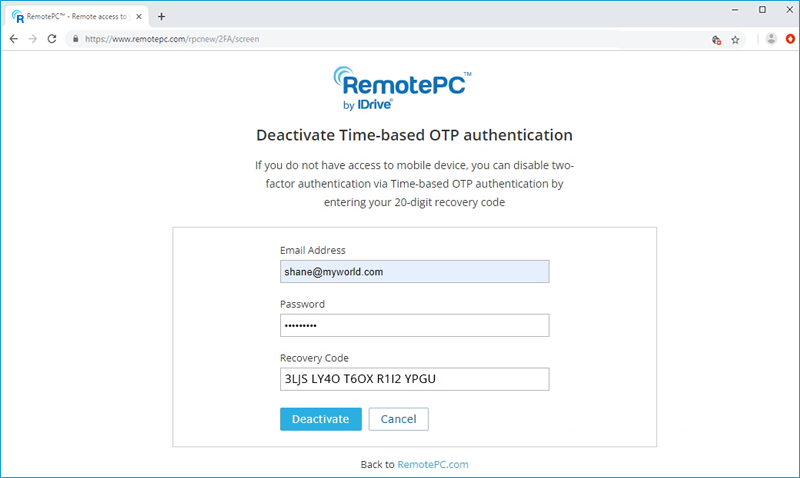
Can I disable two-factor authentication for my RemotePC account with Time based OTP authentication, in case I lost access to my mobile device?
Yes, you can disable two-factor authentication for your RemotePC account with Time based OTP authentication. To disable,
To disable,
- Navigate to RemotePC login screen, enter your username and password, and click 'Login'.
- In the verification code screen that appears, click the link 'I can't access my code'.
- In the 'Recovery Code' field, enter the recovery code received while configuring two-factor authentication for your RemotePC account.
- Click 'Deactivate Time-based OTP Authenticator'.
Trusted devices provide an additional level of security for your RemotePC account. Each time you login to your account from a new device, you are required to authorize it as a Trusted Device. You can thus prevent any unwanted access to your account.
Once you log in to your RemotePC account via a new device for the first time, you will be prompted with the following message:

A device authorization email will be sent to your registered email address. Click the 'Add to trusted devices' button in this email to add the device to the Trusted Devices list. A confirmation message will appear, informing the same.
You can view the list of all your linked devices in the 'Security' tab of your 'My Account' section.
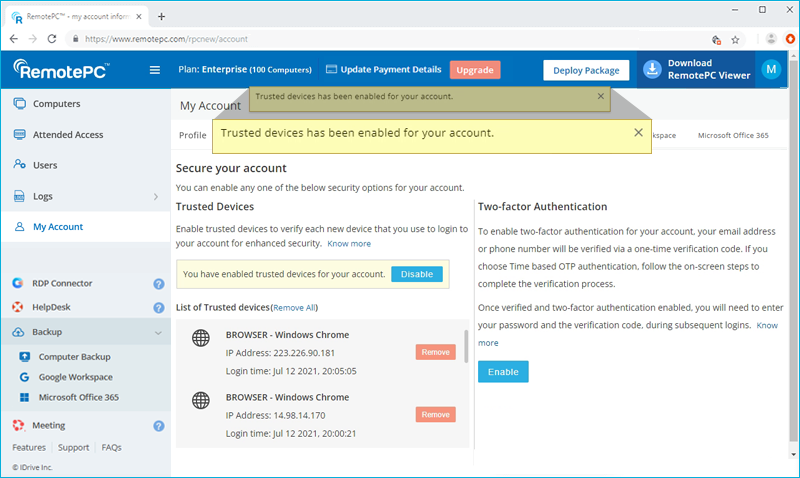
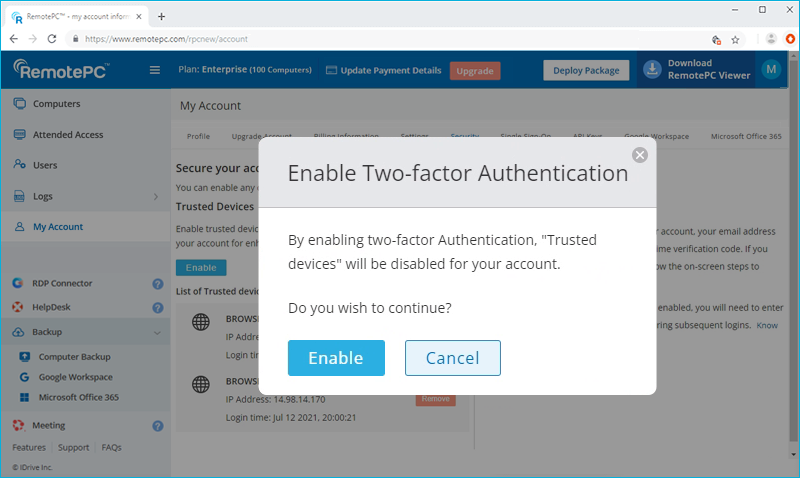
In operation, two-factor verification and trusted devices security features are mutually exclusive. Therefore, at a given time, you can enable either two-factor authentication or trusted devices and not both.
If you attempt to enable two-factor authentication while trusted devices is enabled, a pop-up disclaimer will inform you that trusted devices will be automatically disabled and vice versa.
Yes, you can enable two-factor authentication or trusted devices for new and existing users.
While adding a new user, you can select either the 'Enable trusted devices' or 'Enable two-factor authentication' checkbox in the 'Add User' screen.
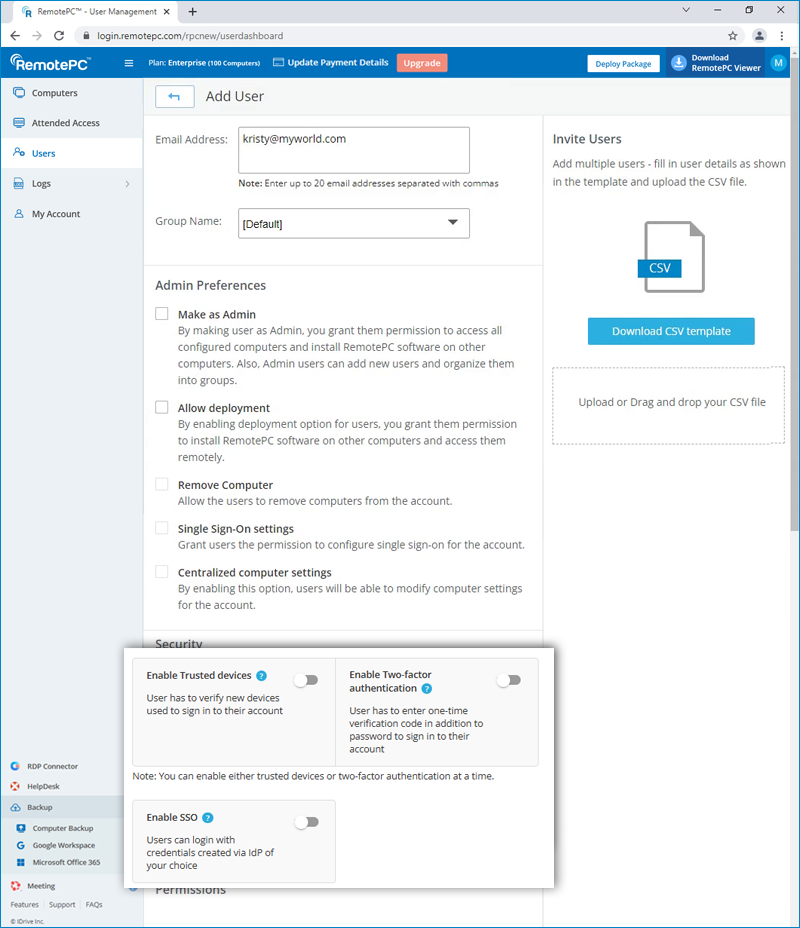
For existing users:
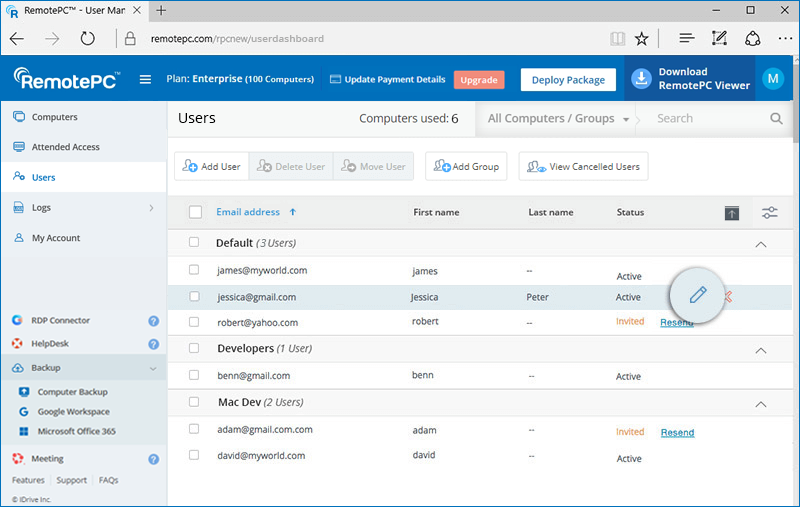
You can open the 'Edit User' screen by clicking  displayed against an existing user, and then select the 'Enable trusted devices' or 'Enable two-factor authentication' checkbox.
displayed against an existing user, and then select the 'Enable trusted devices' or 'Enable two-factor authentication' checkbox.
If two-factor authentication is enabled:
On login your users will be asked to choose a method (Email, SMS or Time-based OTP authentication) for receiving the one-time code. Once they verify the credentials via OTP, the configuration process will be complete.
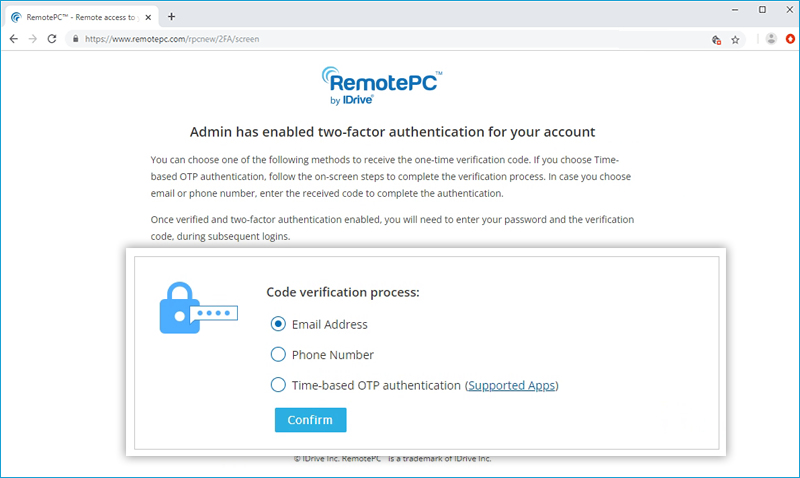
During all subsequent logins, users will need to enter the code sent to their registered email address, phone number or the code displayed in their Google Authenticator app. To change the method of receiving OTP, users can go to 'My Account' > 'Security' > 'Two-factor authentication' and update the preferences from Email Address, Phone Number or Time-based OTP authentication.
Your users will be prompted to authorize every new device at login. They will need to click the 'Add to trusted devices' button in the device authorization mailer they receive.
During two-factor authentication, if you are unable to receive the SMS containing the OTP, you can choose to receive the verification code via email address. Click 'Receive verification code via email address' in the two-factor authentication page. A code will be sent to the registered email address, you can enter the code and complete the verification process.